IT departments are rapacious for any robust or recognized slants that make your own device (BYOD) access of enterprise resources both secure and reliable. Some years ago, everything was very common and there was not so much complexity. Employees usually were not allowed to use their own laptops or mobile devices, which allowed the IT departments to keep everything locked down.
It has been proved in the study that most employees want to use their own device in the workplace. Most of the workers expected that the work environment should be flexible, conducive, giving them the freedom to work. The effective solution only can mitigate the challenges of BYOD.
Challenges of Managing Devices
It is extremely difficult for IT departments to take control over the mobile devices that are usually not wired to the corporate network or not administered by them. At the same time, they have no control over what applications or software are installed, how they behave, how it is secured or what files are downloaded.
Keeping business data along with personal data can be a huge challenge as some employees fail to keep their devices updated. Failing to keep a device updated with latest patches increases the possibility the device being exposed to vulnerabilities.
With an arrival of personal devices in the workplace (BYOD), the possibility of viruses, hacks, and other cybersecurity risks is elevated. In Contrast, hardware run and monitored by the IT department makes company executives and IT folks feel more protected against data breaches and other disastrous security attacks.
IT is faced with questions from employees like –
- Are their device protected by organizational policies?
- Do IT have access to their personal data?
- Will their personal data run risk of being wiped out at the time of leaving the organization?
This raises a host of hugely complex legal complications the company must navigate.
- Do IT have permission to search the device?
- Will the discovered data hold up in an arbitration case?
- If the employee is fired and the company wipes his device, are they liable if personal data also is erased?
As many employees connect their own devices to office network from perimeter network or home network having less or no gateway protection, this increases the chances of vulnerability and attackers.
Many of the mobile companies also customize the OS with own proprietary branding /adware/promotional apps. This directly creates a fertile land for attackers and usually get affected by malware/spyware and several other heuristic attacks.
Hence we need to find a solution to manage such devices, yet provide flexibility of the ease of using these devices from inside and outside the corporate network. Microsoft has the line of protection and management suite to answer most of the above concerns. Microsoft Intune with Mobile Device Management (MDM) is the answer.
To learn more about Netwoven’s Identity & Access Management Capability, Click here.
Why should we Choose Azure Intune as Mobile Device Management?
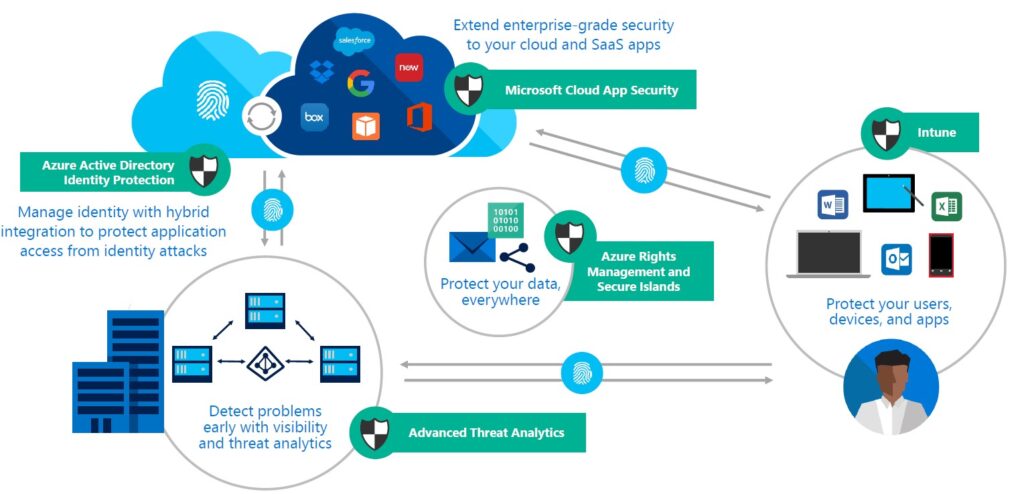
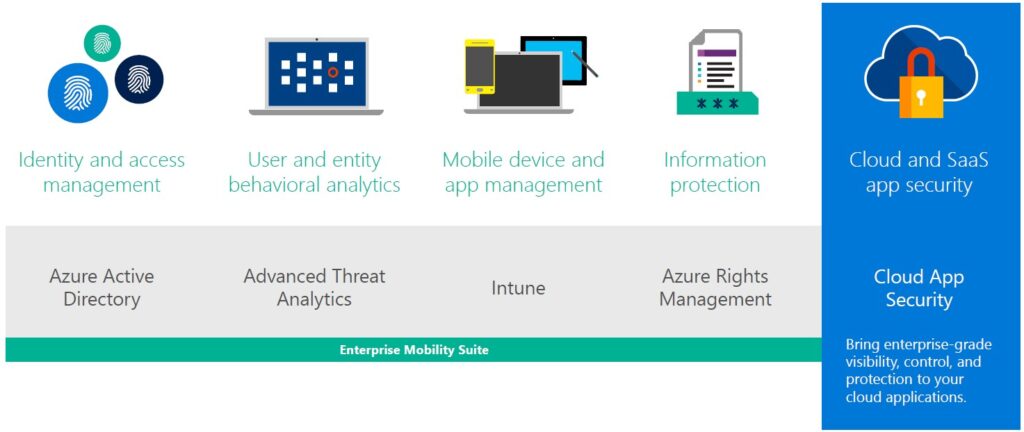
Azure provides a huge ecosystem of security services to customize your need for mobile device management. An enterprise can pick & choose all or some as per their required security level.
Device Management Statistics
As reported by Microsoft, approximately 300,000 domain-joined devices that are managed by System Center Configuration Manager and approximately 125,000 devices using Intune. These includes:
Note:
- 40,000 iOS devices.
- 17,000 Android devices.
- 20,000 Windows Phone devices.
- 34,000 Windows 10 devices.
- 3,000 Mac devices.
- Even the most sophisticated attacks leave behind traces that can form detectable patterns. Every month Microsoft processes a tremendous volume of these signals. In addition, more than 1 billion PCs, service more than 450 billion consumer and enterprise authentications, and analyze more than 200 billion emails for malware and malicious websites.
More Control to IT Team
EMS and Intune provides administrators with the right set of tools and controls to support and manage the diverse ecosystem of mobile devices.

Tackle mobile complexity with flexible management options. EMS allows you to protect the user, device, app, and file levels, giving you an incredible amount of flexibility and choice in how you solve for a variety of needs within your organization. You even have the option to protect corporate data on unmanaged devices, enabling data protection across a wider range of scenarios.
Manage everything from one unified, modern console. Our Azure-based portal gives you a unified EMS administrative experience that allows for streamlined management of core EMS workflows across Azure AD and Intune. You can also manage devices, users, and groups with nearly unlimited scale.

Simplify user lifecycle management. With a single identity across all IT functions, integration with HR applications and the use of dynamic groups you can simplify provisioning of users across application during every phase of their lifecycle in the organization. Manage who has access to what when employees join or leave the company or when they move across teams.
Simplify, automate and integrate workloads. Microsoft Graph API connects developers to the data that drives productivity mail, calendar, contacts, documents, directory, devices, and more. EMS gives you the capability to connect different services and automate workflows and processes between them.
Cloud architecture that just works. As a cloud solution that integrates with your on-premises infrastructure, EMS takes the worry out of maintenance and updates. You get the confidence of knowing that your system is always up to date and ready to scale globally as your needs change.
Deployment planning and ongoing support set you up for success. Netwoven provides you with a specialized skill of certified security engineers and cloud experts help you plan and execute your EMS deployment. And our managed support keeps you running strong day today.
Conclusion
Azure Intune (MDM) is a low-cost product that can be implemented Completely as a cloud solution.
Key Take -Away
- Straight-forward
- Easily Integrates into Configuration Manager
- Few click Administration.
- Rich deep drill down.
- Multiple enrolment options
- Fine Grained policy-based device management
- Flexibility for users to work from anywhere
- Supports popular mobile platforms – Windows, Android & IOS.
Download the Datasheet to learn more about Netwoven’s Information Protection and Compliance service.
Download the Solution Brief to learn how Netwoven’s solution proactively identifies and protects your sensitive data.